Setup and Multi-Factor Authentication
Here at SPU, MFA is a requirement for your account. This is because, while it’s not a “silver bullet,” it still provides additional security and verification, such as a code sent via text message or email, or biometrics like a fingerprint or facial recognition; it helps confirm our identities when logging in.
Just because you receive a prompt or notification for approval, doesn’t mean it’s always you who is logging in. It’s still important that when you receive notifications that you check and make sure you know why you’re getting a prompt and if it’s something you expect to have happen.
Setting up MFA a.k.a. Two-Factor Authentication is a step in the right direction towards protecting yourself and those around you.
Consider turning MFA on for all email accounts, banking, social media, online shopping, and any other location where information about your identity might be stored.
We hope these tips we shared with you today help you stay safter online. Stay tuned throughout October for more ways you can stay safe in our digital world.
As a reminder, CIS will never request your password or other protected information via email.
Keeping your Computer Secure - October 14, 2024
Today we’re going to cover tips on how to keep your personal computer update to date, which is also a way to keep your data safe & secure.
Regularly Install Operating System Updates
Ensuring your device has the latest Operating System (OS) updates is important. If you’re like us, you also have a personal computer and that means you’re the person in charge of determining when and how often you update your computer. By setting your updates to install automatically, you can ensure you have the latest security patches.
Updates not only keep your device working well, but they help close security loopholes and keep you save. Click the links below to learn how to check for updates yourself and ensure you have automatic updates set up.
https://support.apple.com/guide/mac-help/keep-your-mac-up-to-date-mchlpx1065/mac
Encrypt your Computer’s Hard Drive
Encryption is one way to ensure your data is secure and that someone can’t get to your data even if they extract the hard drive from the computer. This is the case for both Windows and Mac users, but if you want to keep your personal data secure, enabling hard drive encryption is one way you can protect yourself from unauthorized access.
Watch this video about BitLocker (Microsoft’s Encryption tool) to learn more about how it works: https://youtu.be/iX8QC2pRuYM?si=5qtlfugkpzByApRu
It’s important to ensure if you turn encryption on, that you read through all the documentation and have your encryption key backed up in a secure location. Without this key, your data may be lost.
https://support.microsoft.com/en-us/windows/bitlocker-overview-44c0c61c-989d-4a69-8822-b95cd49b1bbf
https://support.apple.com/guide/mac-help/protect-data-on-your-mac-with-filevault-mh11785/mac
Keep your Software Up to Date
In addition to keeping your operating system up to date, it’s also important to ensure the software you install on your computer is also kept up to date. Often, you can do this by choosing automatic updates in the application’s menu interface, but if automatic updates aren’t available, add a quarterly reminder to your calendar or task list to check for updates.
https://www.google.com/chrome/update/
Other ways to Keep your Computer Secure
Operating systems have a variety of features that can help you keep your data safe & secure. These might be tools like Microsoft Defender, great for scanning your system for malicious software, firewall settings to prevent unwanted internet traffic and connections to your computer
Stay Protected with Windows Security
https://www.apple.com/macos/security/
https://support.apple.com/guide/security/welcome/web
Install Software from Known Vendors
It’s important to know what you’re installing on your computer and where it comes from. By default, both Mac and PC devices require installation packages to be “digitally signed” by the vendor. You can override these settings and install applications from other places, but it’s still important to properly vet your software choices, paying attention to not only if the company is reputable, but also their Terms of Use & Privacy statements.
https://support.apple.com/guide/mac-help/open-a-mac-app-from-an-unknown-developer-mh40616/mac
If you bought a Windows 11 PC in “S” Mode - which only allows apps from the Microsoft Store, you’ll need to switch out of “S” mode. Please note this is a One-way change. You can learn more at https://support.microsoft.com/en-us/windows/windows-10-and-windows-11-in-s-mode-faq-851057d6-1ee9-b9e5-c30b-93baebeebc85
Retire Old Software & Systems
We all want to save money and often we think of computers in similar terms to the way we think about cars; use it and get as much life out of it as possible before selling it. Unfortunately, this mindset can lead to insecure systems because as the device ages, it will get to a point where the company no longer supports it or creates security patches for it. All software has a life cycle and it’s important to be aware of these, so you can know when to prepare to change software versions or upgrade to a new device with the latest operating system.
One major change that we know about, is Windows 10 coming to the end of its life cycle. As noted by Microsoft on their site: https://learn.microsoft.com/en-us/lifecycle/products/windows-10-home-and-pro on October 14, 2025, there will be no further major releases or monthly patching. If you haven’t thought about upgrading your personal PC yet, now is a good time to start planning that process.
https://learn.microsoft.com/en-us/lifecycle/
https://support.apple.com/en-us/100100
Exploring Phishing and Social Engineering Attacks - October 21, 2024
Last week we talked about your computer and ways you could keep the device safe and secure. This week let’s dive into Phishing and Social Engineering a bit more.
What is Social Engineering?
In a social engineering attack, an attacker uses human interaction (social skills) to obtain or compromise information from an organization or its computer systems. This even happens at SPU. The attacker may seem unassuming and respectable. They may even claim to be someone you know or a name you recognize, maybe even a position or job title that sounds legitimate. Just by asking questions, they may be able to piece enough information together to try to infiltrate and if they can’t get what they need through one avenue, then they’ll try another.
What is a Phishing Attack?
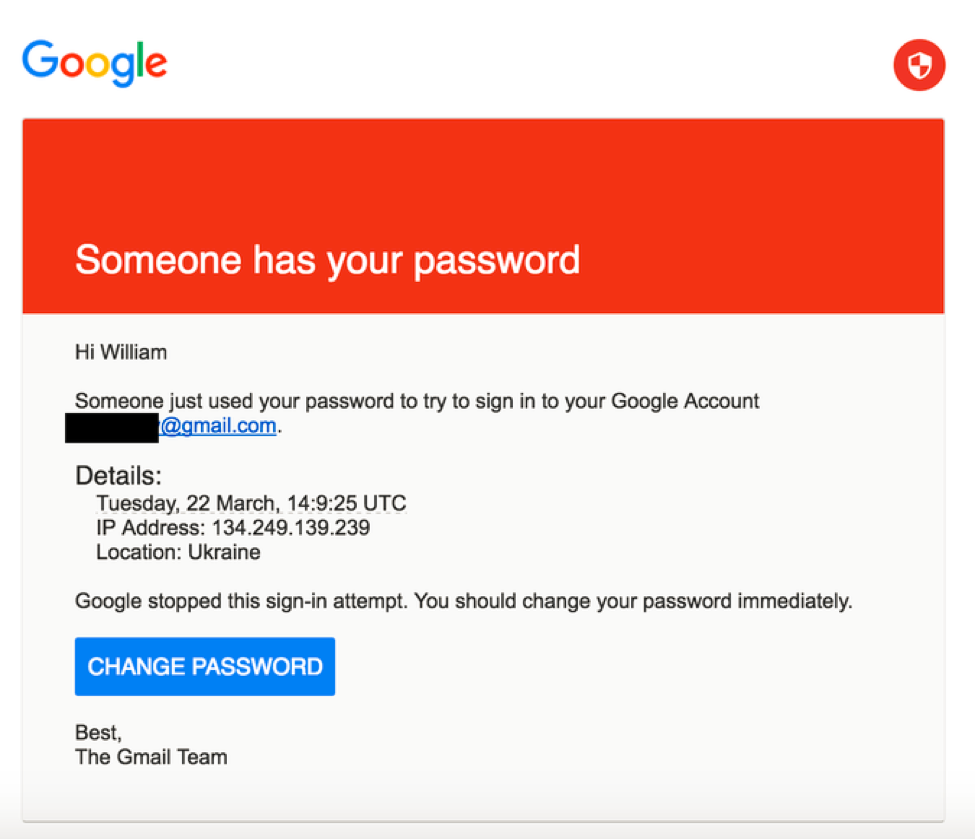
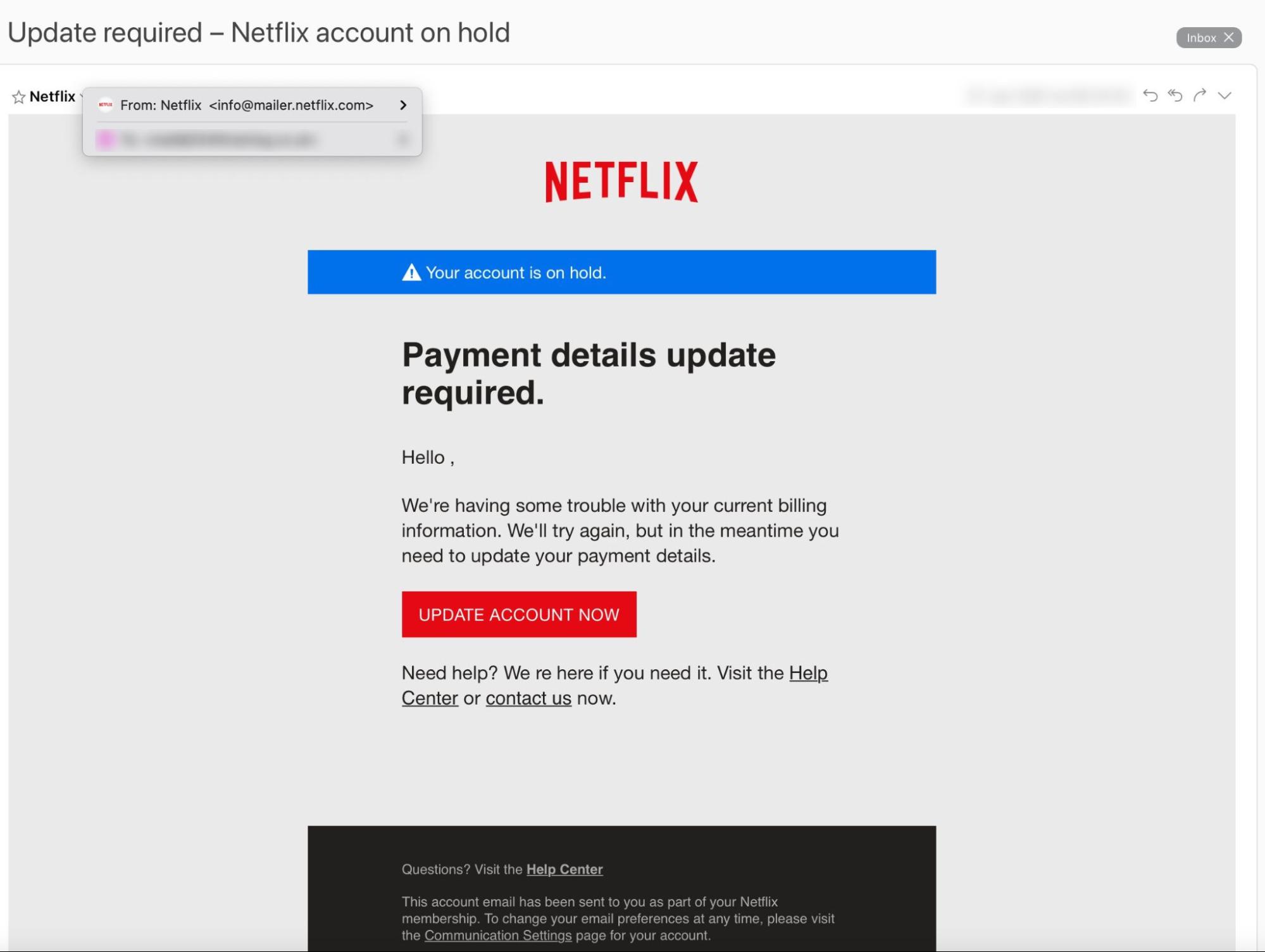
A phishing attack is a form of social engineering - these attacks typically utilize email or malicious websites to solicit information by posing as a trustworthy organization or person. For example, an email you receive may appear to be from a bank or other reputable company; sometimes a person offering a job. When you respond, attackers then gain access to all of the accounts and information you shared and, in some cases, may use this information to threaten you.
What are Common Indicators of Phishing Attempts?
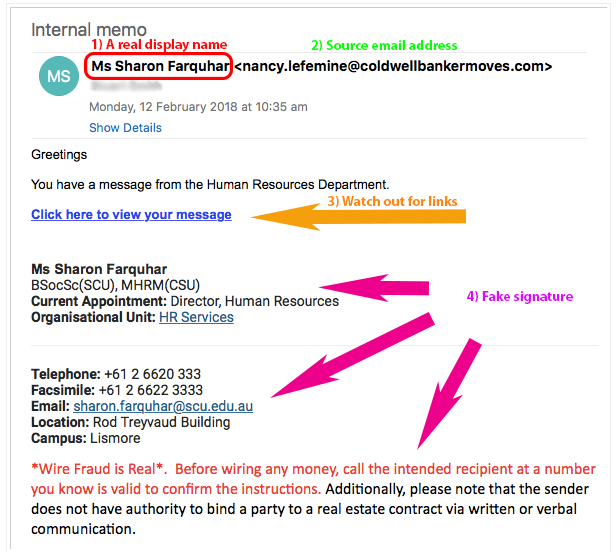
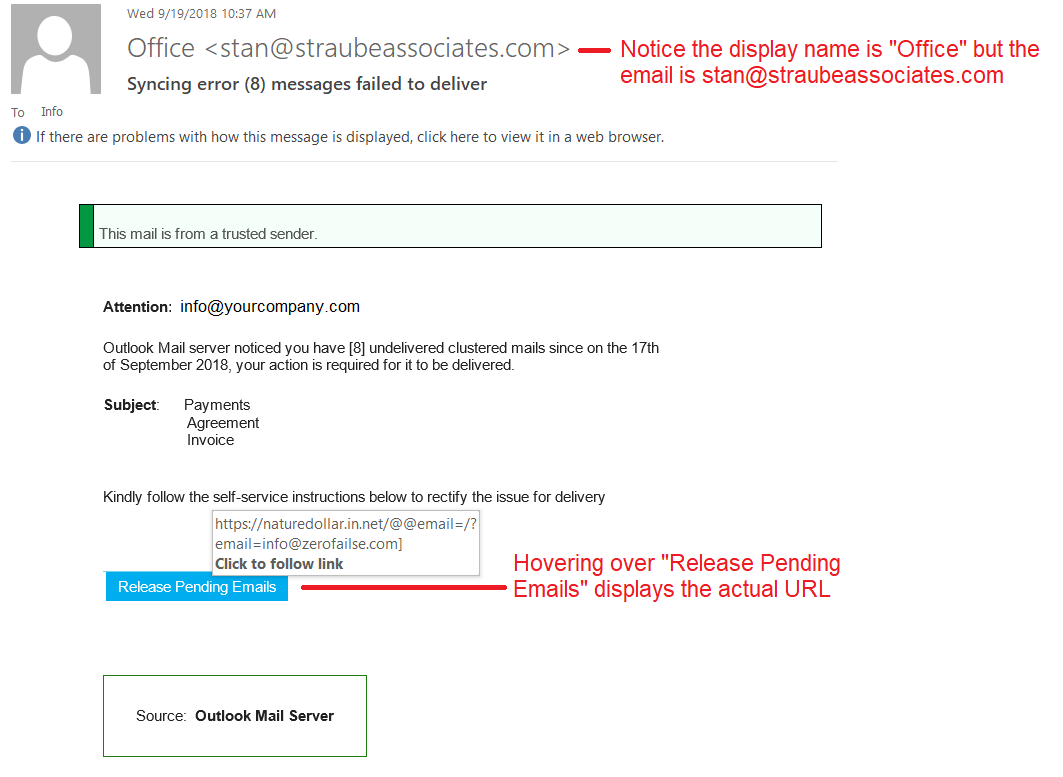
Suspicious sender's address. The sender's address may imitate a legitimate business. Cybercriminals often use an email address that closely resembles one from a reputable company by altering or omitting a few characters.
Generic greetings and signature. Both a generic greeting—such as "Dear Valued Customer" or "Sir/Ma'am"—and a lack of contact information in the signature block are strong indicators of a phishing email. A trusted organization will normally address you by name and provide their contact information.
Spoofed hyperlinks and websites. If you hover your cursor over any links in the body of the email, and the links do not match the text that appears when hovering over them, the link may be spoofed. Malicious websites may look identical to a legitimate site, but the URL may use a variation in spelling or a different domain (e.g., .com vs. .net). Additionally, cybercriminals may use a URL shortening service to hide the true destination of the link.
Spelling and layout. Poor grammar and sentence structure, misspellings, and inconsistent formatting are other indicators of a possible phishing attempt. Reputable institutions have dedicated personnel that produce, verify, and proofread customer correspondence.
Suspicious attachments. An unsolicited email requesting a user download and open an attachment is a common delivery mechanism for malware. A cybercriminal may use a false sense of urgency or importance to help persuade a user to download or open an attachment without examining it first.
How do you Avoid Being a Victim?
Be suspicious of unsolicited phone calls, visits, or email messages from individuals asking about employees or other internal information. If an unknown individual claims to be from a legitimate organization, try to verify his or her identity directly with the company.
Do not provide personal information or information about your organization, including its structure or networks, unless you are certain of a person's authority to have the information.
Do not reveal personal or financial information in email, and do not respond to email solicitations for this information. This includes following links sent in email.
Don't send sensitive information over the internet before checking a website's security. (See Protecting Your Privacy for more information.)
Pay attention to the Uniform Resource Locator (URL) of a website. Look for URLs that begin with "https"—an indication that sites are secure—rather than "http."
Look for a closed padlock icon—a sign your information will be encrypted.
If you are unsure whether an email request is legitimate, try to verify it by contacting the company directly. Do not use contact information provided on a website connected to the request; instead, check previous statements for contact information. Information about known phishing attacks is also available online from groups such as the Anti-Phishing Working Group. (See the APWG eCrime Research Papers).
Install and maintain anti-virus software, firewalls, and email filters to reduce some of this traffic. (See Understanding Firewalls for Home and Small Office Use, Protecting Against Malicious Code, and Reducing Spam for more information.)
Take advantage of any anti-phishing features offered by your email client and web browser.
Enforce multifactor authentication (MFA). (See Supplementing Passwords for more information.)
What Should you do if you’re a Victim of Phishing?
If you believe you might have revealed sensitive information about your yourself or SPU, immediately report it to the CIS HelpDesk so we can lock your account and prevent further access.
If you believe your financial accounts may be compromised, contact your financial institution immediately and close any accounts that may have been compromised. Watch for any unexplainable charges to your account.
Immediately change any passwords. If you used the same password for multiple resources, make sure to change it for each account, and do not use that password in the future.
Consider filing a report with the Office of Safety & Security (OSS). If money was stolen or you’re being threatened, OSS can work with local authorities to file reports and recover stolen property. Call 206-281-2922 or email securityinfo@spu.edu.
Watch for other signs of identity theft. (See Preventing and Responding to Identity Theft for more information.)
If you’re ever not sure, reach out to the CIS HelpDesk at help@spu.edu or at 206-281-2982 so we can assist you.
Source: Avoiding Social Engineering and Phishing Attacks. February 2021. Retrieved, October 2024. https://www.cisa.gov/news-events/news/avoiding-social-engineering-and-phishing-attacks
Outdoor Wifi Locations
Outdoor WiFi locations are available in Tiffany Loop, Martin Square, and in front of the C-Store.
SPU Online Services
All of your online services can be found by clicking on the icon in the top right corner of any SPU webpage and navigating to the Students tab.
Microsoft Office 365 for Education
There are many Microsoft Office products available to you as an SPU student, including:
Your SPU Email
Check your SPU email frequently for important campus-wide communications and information from your professors about your classes. See here for help with configuring your SPU email across all your devices (computers, tablets, phones, etc).
Microsoft Teams
Microsoft Teams is a great collaboration tool that all SPU students have access to. Instant message your classmates, host a study group online, share files, and more. See here for more information: Study Groups In-Person and Online.
OneDrive for Business
As an SPU student you receive 1 TB (terabyte) of cloud storage space in OneDrive for Business. Your documents can be stored securely here and your account is accessible from any of your devices, on or off-campus. Documents can also be shared with others for group collaboration. Learn more here.
Microsoft Office Suite
Current students may obtain the latest version of Microsoft Office for Windows or Mac through the Microsoft Student Advantage Program. There is no cost to install the software on up to 5 personal devices, including your computer (PC or Mac), tablet (iPad or Android), or mobile phone (iPhone or Android). The Office Suite provides powerful productivity tools including: Word, Excel, PowerPoint, OneDrive, and Outlook. Learn more here.
More Office Apps
In addition to the Microsoft Office Suite (Word, Excel, PowerPoint, OneDrive, and Outlook) there are numerous apps that are available for you to use, such as Lists, Project, Visio, Planner and more. Log into your account to see what's available today.
Minecraft for Education
You have access to Minecraft at no additional cost through your SPU account. See here for more information.
Printing and Copying
SPU provides a campus-wide printing/copying program for students. There are Multi-Function Printers (MFPs) located across campus for your use. You can submit print jobs via the web from on or off campus and print them from any MFP once arriving on campus. You can also print directly from your computer or a USB flash-drive, copy, and scan to email. Document scanning on the MFPs is free and does not require print credit. Detailed instructions are posted at each MFP and on the CIS website: MFP Student Printing.
Print Credits
You receive print credits at the beginning of each quarter that accumulates through the academic school year as part of your Technology Fee.
Students enrolled in 12 or more credits get $5.00 per quarter
Students enrolled in 11 credits or less get $2.50 per quarter.
When print credit has been used up, you can use Falcon Funds on your SPU ID Card for additional printing.
Watch Out for Scams!
While many illegitimate messages are filtered out of your inbox some may still get through. SPU will NEVER ask you to send or verify your login credentials or other personal/confidential information via email. Your account credentials should not be shared with anyone!
Job Scams
You've probably already received several emails scam offering an employment opportunity from someone who appears to be associated with SPU. Please delete these messages and do not respond. All legitimate jobs at the university are posted on SPU's Handshake platform. Employers on Handshake are vetted to guarantee their trustworthiness. Here is a blog post with more information to help you identify and avoid employment scammers. If you have any questions about the legitimacy of an email message, please forward it to help@spu.edu.
Phishing
Phishing scams often come in the form of email messages attempting to steal your username and password. PLEASE DO NOT reply to these messages or follow web links where you must confirm or enter your username and password. If you have questions about the legitimacy of a message, please forward it to help@spu.edu and we can assist. See this Cybersecurity Awareness Month blog post about phishing for additional information.
Password
To ensure your passwords are as secure as possible, make them at least 16 characters long, use a random combination of mixed-case letters, numbers, and symbols—or create a memorable passphrase consisting of 4 to 7 unrelated words with or without spaces—and make sure to use a unique password for each of your accounts, such as k8dfh8c@Pfv0gB2 for your bank, legal tiny facility freehand probable enamel for your email account, and e246gs%mFs#3tv6 for your social media, thereby significantly enhancing your overall online security.
Peer-to-Peer File Sharing and Copyright Compliance
File sharing software that copies and distributes songs, movies, videos, games, and software applications without the permission of the owner is a Copyright Law violation that can subject you to criminal and civil liability. Content owners use technological means to track the file sharing of their intellectual property on the Internet. SPU is required by law to inform you if we are aware, you have violated copyright law and must provide your information to copyright owners for legal action if you do not cease illegal activity. You are responsible for the activities of your computer when connected to the campus network. See Copyright Basics and DMCA Copyright Compliance / Peer-to-Peer File Sharing for more information about copyright compliance.
Update Your Emergency Contacts and SPU Alert Info
It is important to be made aware of campus emergencies in real-time, as information is available.
SPU-Alert is the emergency alert system used to notify you of campus emergencies via text, email, and voice calls. We need your current contact information so that we can send you alerts during a campus emergency.
Emergency Contact Information includes the contact details SPU should use in the event that an emergency situation happens to you.
The beginning of the school year is a great time to review and update your information. Log into the Banner Information System, go to the Personal Menu, update your information on the Emergency Alert System and Emergency Contact Information pages.
SPU will NEVER ask you to send your login credentials or other personal/confidential information via email. Your account credentials should never be shared with anyone.
Guest WiFi
Guest WiFi is available for parents, friends, and campus guests. Connect to the network ID called SPU-Guests, then launch a web browser and follow the guest registration instructions. Guests must provide a valid, non-SPU email address or a text-messaging cell phone number for registration. Guest WiFi is bandwidth-limited. SPU students should use the network named SPU-Wireless for high speed internet access. Learn more here.
Campus Printing and Personal Printers
There are Multi-Function Printers (MFPs) available to you in many locations on campus. Each quarter you will receive credits to use towards printing and copying. We encourage all students to use these MFPs rather than bring a personal printer on campus. If you do need a personal printer on campus, please know that your wireless printers will not work on the campus wireless network. Disable the wireless networking on your printer and use a USB cable (available at the SPU Bookstore or other stores) to connect to your computer.
For Information about on-campus printing and copying see: Student Printing
SPU will NEVER ask you to send your login credentials or other personal/confidential information via email. Your account credentials should not be shared with anyone. |
Remote Labs Shift
Students:
SPU Students have remote access to Windows Computer Labs that can be used to access specialized lab software from most computers. This software had a name change and was originally known as LabStats, is now renamed as RemoteLabs.
The application facilitates quicker access to the device and redirects you to the remote lab page. For detailed instructions on how to use this resource, please visit the Remote Lab Access wiki page, or follow the link here.
October is Cybersecurity Awareness Month - CSA
It is CIS's responsibility to share some vital information about how to be safe while using the internet and managing yours and students' information.
Over the next few weeks, CIS will be releasing a weekly blog post that expands on four core topics for this year's CSA month: Phishing, Social Engineering (whaling), Passphrases for passwords, and Ransomware.
At the end of the month, there will be a quiz released to employees and students. Receiving 100% on the quiz will automatically enter the user into a raffle. The raffle will have two winners, one student and one employee, who will each receive a prize* from CIS!
Keep an eye out for the first blog post on October 9, and then every following Monday until the end of the month!
*Please note that prizes will be ordered once they are selected by the prize-winners. CIS will contact prize-winners when the prizes are ready to be picked up from the HelpDesk.
Security Awareness Week 1: Phishing emails
What is Phishing?
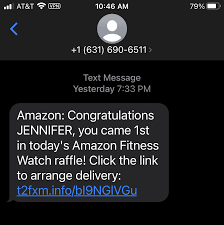
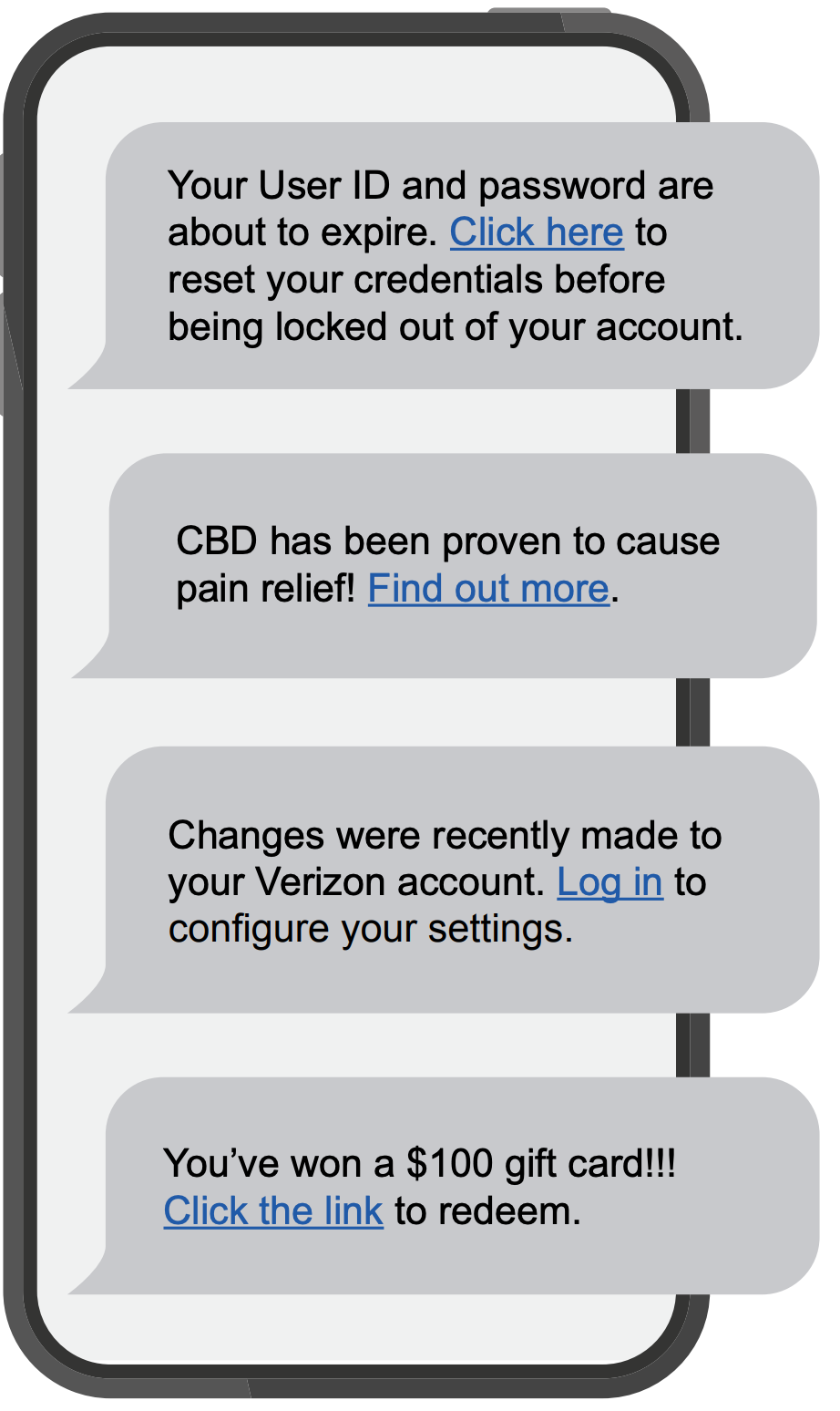
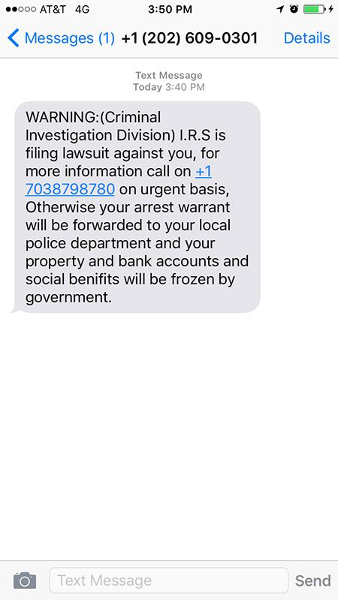
Often carried out over email -- although the scam has now spread beyond suspicious emails to phone calls (so-called "vishing"), social media, SMS messaging services (aka "smishing"), and apps -- a basic Phishing attack attempts to trick the target into doing what the scammer wants.
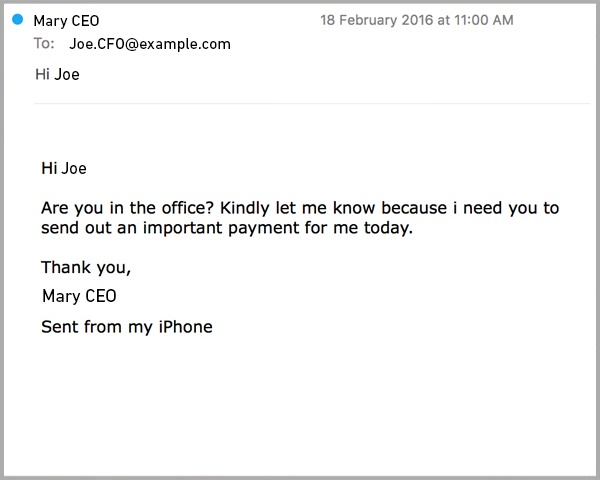
Exactly what the scammer wants can vary wildly between attacks. It might be handing over passwords to make it easier to hack a company or person, or sending payments to fraudsters instead of the correct account. This information is often stolen by making requests that look entirely legitimate -- like an email from your boss, so you don't think twice about doing what is asked.
How would you identify a Phishing email?
Emails that contain the following should be approached with extreme caution, as these are common traits of phishing email:
- Urgent action demands.
- Multiple sources in the from email address line.
- Poor grammar and spelling errors.
- An unfamiliar greeting or salutation.
- Requests for login credentials, payment information, or sensitive data.
- Offers that are too good to be true.
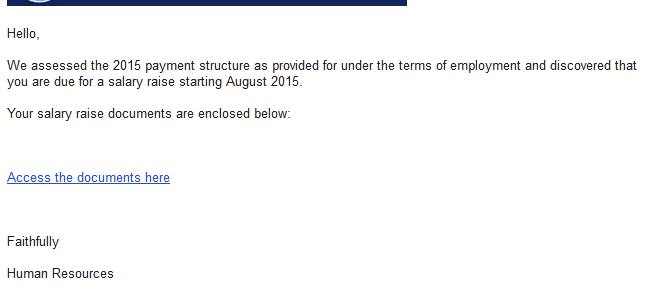
Phishing is also a popular method for cyber attackers to deliver malware by encouraging victims to download a weaponized document or visit a malicious link that will secretly install the malicious payload on the person's computer. These kind of attacks mostly are trying to distribute a trojan malware, ransomware . These cyber hackers are hoping you don't look to deep into the email, that you just gloss over the details and click on the link, or download the attachment. Below is a screenshot of a phishing email, and you can see just how tricky they can be.
Why is Phishing called Phishing?
The overall term for these scams -- Phishing -- is a modified version of the word 'fishing' except in this instance the one doing this fishing is a scammer and they're trying to catch you and reel you in with their sneaky email lure. In most cases, they will send out many of these lures.
FUN FACT! - Why is Phishing spelled with a "Ph"?
The “ph” spelling of phishing is influenced by an earlier word for an illicit act: phreaking, which involves fraudulently using an electronic device to avoid paying for telephone calls. The people who perpetrated phreaking were called “Phreaks,” and since phreaks and hackers were closely linked, the “ph” spelling was used to denote the phishing scams involving these underground groups. Pretty cool!
We hope by sharing these resources with you, that you will have the tools and information necessary to make informed decisions when using the Internet.
Security Awareness Week 2: Ransomware
The CISA defines Ransomware as a "form of malware designed to encrypt files on a device, rendering any files and the systems that rely on them unusable. Malicious actors then demand ransom in exchange for decryption."
Ransomware can be planted into a network using many methods, like Phishing and Social Engineering. Once it is planted, hackers locate and secure access to important files and move those files to a secure network of their own.
Oftentimes, a hacker needs only access into a network, and can gain such access in a myriad of ways. For example:
- By sending phishing emails requesting login information or containing malicious code(as we have seen in last week's post)
- Looking for weaknesses within your network's security
- Users are redirected to a suspicious website that infects their computer by browsing or prompts for them to download files off the internet.
Computer Safety Tips:
Regularly back up important and sensitive data to a separate drive.
Install and regularly update antivirus software on your device.
Exercise caution when following links in emails, text messages, and websites.
Be mindful of what files your are downloading from the internet and avoid suspicious sites.
SPU Employees SPU-Managed Devices:
Software and application patches, anti-virus updates, data backups, mandatory browser and security settings are all implemented by CIS and enforced on your school-issued devices.
However, it is still essential for all employees to use their best judgement when viewing emails and websites.
Example 1. Fake websites
A cyber-criminal will design a carefully-worded phishing email which includes a link to a spoofed version of a popular website. The website imitates the layout of the original site to trick the victim into entering their account credentials.
Example 2. CEO Fraud
An attacker will take control of an email address familiar to the employee, such as their company’s CEO, Human Resources Manager, or IT admin. The hacker will assume this individual’s identity and ask the user to complete an urgent action, such as transferring funds, updating their personal information, or installing a new app.
Example 3. Malware
In these types of phishing attacks, an attacker will try to trick an employee into clicking on a malicious email attachment. Usually, this type of attack is carried out with a fake invoice or delivery notification.
If you think that the email may be legit, go to a link that you know is safe (one that you have save for the company) and log in from there. Or, you can always call the company and confirm or deny the validity of the email you received.
REMEMBER
If you don't recognize the sender, NEVER click on the attachments or links!
Example 4. Smishing
An SMS-based phishing attack in which a hacker will send an SMS or voice message asking the recipient to click on a link to accept a gift, change your password or call a number. The link will take them to a phishing website that they will use to try and gather more information from you.
Also, the link you click on could have malware in it. What does that mean? It could install a program on your phone that will allow the hacker to gain access to all your personal information, e.g. contacts, passwords, email, photos.
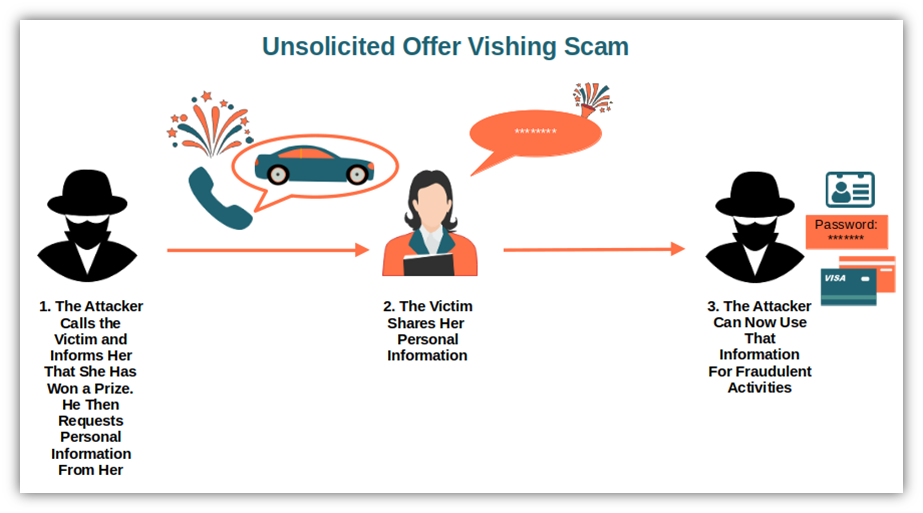
Example 5. Vishing
An unknown caller will call the victim and or leave a voicemail urging them to phone them back and hand over personal information, usually by impersonating someone from a trusted company.
The most common type of this is a Tech Support Call.
This attack is widespread in large companies where employees might not know or have met members of the tech support department. Scammers will pretend they need to do a computer update or repair and ask for the victim’s password to do it.
Education is key to beating these attacks. Frequently remind users that you will never ask them to divulge their password over the phone and that they shouldn’t do so under any circumstance.
Creating a Strong Passphrase
It is also important for users to use a strong Passphrase or password for securing your account. A strong password will protect your account while also not containing any personally identifiable words; like your mother's maiden name or your childhood pet. It is also important to use a strong or complex password, as a more simple passphrase can be easily guessed.
Here are some key things to follow when creating a password:
- Use a combination of numbers, capitalization and special characters.
- Use a longer passphrase that you can easily remember.
- Don't use a password you have used before, or a slight variation of a pre-existing password.
Do NOT write down OR your share your SPU password with anyone.
Password Managing
If you are worried about keeping track of your passwords, use a password manager that will keep track and record all of your passwords and where they are used. It is also likely that your phone or Google account will have password tracking enabled.
For more information on SPU's Password Policies, please select here.
Cybersecurity Awareness Month Quizzes
Thank you for joining us for this year's Cybersecurity Awareness month as we covered Phishing, Ransomware, Social Engineering (Spear Phishing), Passphrases, and Canary Files.
If you have questions or concerns about the topics covered, or would like to learn more, a student technician with the HelpDesk would be more than happy to assist! You can contact the HelpDesk by phone at 206.281.2982 or by email at help@spu.edu.
As a reminder, we are offering one quiz for Faculty and Staff and one quiz for Students to test their knowledge on the topics we covered this month. The quiz will remain open until November 15th, 2023.
A Few Rules to Follow:
- One quiz attempt per individual.
- A student may not take the employee quiz and employees may not take the student quiz.
- Only scores of 100% will be automatically entered into the raffle.
- Prizes will only be given out to the winning individual(s) after they have made their *selection.
- One prize per winner.
*Raffle winners will be contacted by CIS and choose their prize from the available options. Options include bluetooth speakers and/or gift cards.
Faculty and Staff Quiz Here
Student Quiz Here
Guest WiFi
Guest WiFi is available for parents, friends, and campus guests. Connect to the network ID called SPU-Guests , then launch a web browser and follow the guest registration instructions. Guests must provide a valid, non-SPU email address or a text-messaging cell phone number for registration. Guest WiFi is bandwidth-limited. SPU students should use the network named SPU-Wireless for high speed internet access. Learn more here .
Outdoor Wifi Locations
Outdoor WiFi locations are available in Tiffany Loop, Martin Square, and in front of the C-Store.
SPU Online Services
All of your online services can be found by clicking on the icon in the top right corner of of any SPU webpage and navigating to the Students tab.
Microsoft Office 365 for Education
There are many Microsoft Office products available to you as an SPU student, including:
Microsoft Teams
Microsoft Teams is a great collaboration tool that all SPU students have access to. Instant message your classmates, host a study group online, share files, and more. See here for more information: Study Groups In-Person and Online .
OneDrive for Business
As an SPU student you receive ample cloud storage space in OneDrive for Business. Your documents can be stored securely here and your account is accessible from any of your devices, on or off-campus. Documents can also be shared with others for group collaboration. Learn more here .
Microsoft Office Suite
Current students may obtain the latest version of Microsoft Office for Windows or Mac through the Microsoft Student Advantage Program. There is no cost to install the software on up to 5 personal devices, including your computer (PC or Mac), tablet (iPad or Android), or mobile phone (iPhone or Android). The Office Suite provides powerful productivity tools including: Word, Excel, PowerPoint, OneDrive, and Outlook. Learn more here .
More Office Apps
In addition to the Microsoft Office Suite (Word, Excel, PowerPoint, OneDrive, and Outlook) there are numerous apps that are available for you to use, such as Lists, Project, Visio, Planner and more. Log into your account to see what's available today .
Minecraft for Education
You have access to Minecraft at no additional cost through your SPU account. See here for more information.
Printing and Copying
SPU provides a campus-wide printing/copying program for students. There are Multi-Function Printers (MFPs) located across campus for your use. You can submit print jobs via the web from on or off campus and print them from any MFP once arriving on campus. You can also print directly from your computer or a USB flash-drive, copy, and scan to email. Document scanning on the MFPs is free and does not require print credit. Detailed instructions are posted at each MFP and on the CIS website: MFP Student Printing.
Print Credits
You receive print credits at the beginning of each quarter that accumulates through the academic school year as part of your Technology Fee.
- Students enrolled in 12 or more credits get $5.00 per quarter
- Students enrolled in 11 credits or less get $2.50 per quarter.
- When print credit has been used up, you can use Falcon Funds on your SPU ID Card for additional printing.
Watch Out for Scams!
While many illegitimate messages are filtered out of your inbox some may still get through. SPU will NEVER ask you to send or verify your login credentials or other personal/confidential information via email. Your account credentials should not be shared with anyone!
Job Scams
You've probably already received several emails scam offering an employment opportunity from someone who appears to be associated with SPU. Please delete these messages and do not respond. All legitimate jobs at the university are posted on SPU's Handshake platform . Employers on Handshake are vetted to guarantee their trustworthiness. Here is a blog post with more information to help you identify and avoid employment scammers. If you have any questions about the legitimacy of an email message please forward it to help@spu.edu.
Phishing
Phishing scams often come in the form of email messages attempting to steal your username and password. PLEASE DO NOT reply to these messages or follow web links where you must confirm or enter your username and password. If you have questions about the legitimacy of a message, please forward it to help@spu.edu and we can assist. See this CyberSecurity Awareness Month blog post about phishing for additional information.
Peer-to-Peer File Sharing and Copyright Compliance
File sharing software that copies and distributes songs, movies, videos, games, and software applications without the permission of the owner is a Copyright Law violation that can subject you to criminal and civil liability. Content owners use technological means to track the file sharing of their intellectual property on the Internet. SPU is required by law to inform you if we are aware, you have violated copyright law and must provide your information to copyright owners for legal action if you do not cease illegal activity. You are responsible for the activities of your computer when connected to the campus network. See Copyright Basics and DMCA Copyright Compliance / Peer-to-Peer File Sharing for more information about copyright compliance.
Update Your Emergency Contacts and SPU Alert Info
It is important to be made aware of campus emergencies in real-time, as information is available.
- SPU-Alert is the emergency alert system used to notify you of campus emergencies via text, email, and voice calls. We need your current contact information so that we can send you alerts during a campus emergency.
- Emergency Contact Information includes the contact details SPU should use in the event that an emergency situation happens to you.
The beginning of the school year is a great time to review and update your information. Log into the Banner Information System , go to the Personal Menu , update your information on the Emergency Alert System and Emergency Contact Information pages.
SPU will NEVER ask you to send your login credentials or other personal/confidential information via email. Your account credentials should never be shared with anyone.