October - Cybersecurity Awareness Month 2023
October is Cybersecurity Awareness Month - CSA
It is CIS's responsibility to share some vital information about how to be safe while using the internet and managing yours and students' information.
Over the next few weeks, CIS will be releasing a weekly blog post that expands on four core topics for this year's CSA month: Phishing, Social Engineering (whaling), Passphrases for passwords, and Ransomware.
At the end of the month, there will be a quiz released to employees and students. Receiving 100% on the quiz will automatically enter the user into a raffle. The raffle will have two winners, one student and one employee, who will each receive a prize* from CIS!
Keep an eye out for the first blog post on October 9, and then every following Monday until the end of the month!
*Please note that prizes will be ordered once they are selected by the prize-winners. CIS will contact prize-winners when the prizes are ready to be picked up from the HelpDesk.
You can champion Cybersecurity Awareness Month by practicing and sharing the information we share this month with your friends and family. Each October, we try to raise awareness about digital security and empower everyone to protect their personal data from digital forms of crime.
Now in its 20th year, Cybersecurity Awareness Month continues to build momentum and impact. It is co-led by the National Cybersecurity Alliance and the Cybersecurity and Infrastructure Agency (CISA).
This year’s theme is: Staying Safe Online
– because while cybersecurity may seem like a complex subject, ultimately, it’s really all about people.
Online Safety Basics - Learn how to protect yourself, your family and devices with these tips and resources.

Security Awareness Week 1: Phishing emails
What is Phishing?
Often carried out over email -- although the scam has now spread beyond suspicious emails to phone calls (so-called "vishing"), social media, SMS messaging services (aka "smishing"), and apps -- a basic Phishing attack attempts to trick the target into doing what the scammer wants.
Exactly what the scammer wants can vary wildly between attacks. It might be handing over passwords to make it easier to hack a company or person, or sending payments to fraudsters instead of the correct account. This information is often stolen by making requests that look entirely legitimate -- like an email from your boss, so you don't think twice about doing what is asked.
How would you identify a Phishing email?
Emails that contain the following should be approached with extreme caution, as these are common traits of phishing email:
Urgent action demands.
Multiple sources in the from email address line.
Poor grammar and spelling errors.
An unfamiliar greeting or salutation.
Requests for login credentials, payment information, or sensitive data.
Offers that are too good to be true.
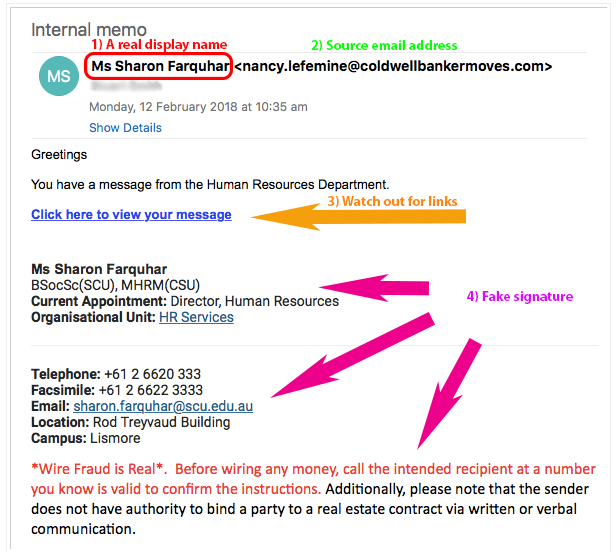
Phishing is also a popular method for cyber attackers to deliver malware by encouraging victims to download a weaponized document or visit a malicious link that will secretly install the malicious payload on the person's computer. These kind of attacks mostly are trying to distribute a trojan malware, ransomware . These cyber hackers are hoping you don't look to deep into the email, that you just gloss over the details and click on the link, or download the attachment. Below is a screenshot of a phishing email, and you can see just how tricky they can be.
Why is Phishing called Phishing?
The overall term for these scams -- Phishing -- is a modified version of the word 'fishing' except in this instance the one doing this fishing is a scammer and they're trying to catch you and reel you in with their sneaky email lure. In most cases, they will send out many of these lures.
FUN FACT! - Why is Phishing spelled with a "Ph"?
The “ph” spelling of phishing is influenced by an earlier word for an illicit act: phreaking, which involves fraudulently using an electronic device to avoid paying for telephone calls. The people who perpetrated phreaking were called “Phreaks,” and since phreaks and hackers were closely linked, the “ph” spelling was used to denote the phishing scams involving these underground groups. Pretty cool!
We hope by sharing these resources with you, that you will have the tools and information necessary to make informed decisions when using the Internet.
Security Awareness Week 2: Ransomware
The CISA defines Ransomware as a "form of malware designed to encrypt files on a device, rendering any files and the systems that rely on them unusable. Malicious actors then demand ransom in exchange for decryption."
Ransomware can be planted into a network using many methods, like Phishing and Social Engineering. Once it is planted, hackers locate and secure access to important files and move those files to a secure network of their own.
Oftentimes, a hacker needs only access into a network, and can gain such access in a myriad of ways. For example:
By sending phishing emails requesting login information or containing malicious code(as we have seen in last week's post)
Looking for weaknesses within your network's security
Users are redirected to a suspicious website that infects their computer by browsing or prompts for them to download files off the internet.
Ransomware Double Attack
A double attack occurs when hackers gain access to a network, move that network's files onto a network they control, then encrypt the data and demand a ransom for a user to regain access and/or to prevent the public publication of those files. The risk: if the ransom is not met, the hackers will sell your data or publish it online.
Unfortunately, users are not typically aware of the attack until they are notified, often by a pop-up declaring the infection and demanding a ransom to receive the decryption key.
Regarding personal data files, law enforcement agencies advise against paying the ransom on such accounts. However, if you don’t have a good back up system, it may be cheaper to pay the ransom to regain access and return your important data.
Computer Safety Tips:
Regularly back up important and sensitive data to a separate drive.
Install and regularly update antivirus software on your device.
Exercise caution when following links in emails, text messages, and websites.
Be mindful of what files your are downloading from the internet and avoid suspicious sites.
SPU Employees SPU-Managed Devices:
Software and application patches, anti-virus updates, data backups, mandatory browser and security settings are all implemented by CIS and enforced on your school-issued devices.
However, it is still essential for all employees to use their best judgement when viewing emails and websites.
If you believe your system is compromised, we urge you to do the following:
Turn off your device.
Disconnect from the internet.
Disconnect your device from any and all external attachments (e.g., usb drives).
Call or email the CIS HelpDesk immediately (206-281-2982 or help@spu.edu)

Security Awareness Week 3: Spear Phishing emails
Spear Phishing is when a cyber-criminal sends an individual an email, SMS message, or voice call, that is designed to manipulate the user into providing the criminal with their login credentials, personal details, or to transfer money.
These types of scams are highly effective because the attackers will typically impersonate the recipient’s boss, colleague, friend, family member, bank, or popular online store to make them feel at ease into giving over sensitive information. (Don't be fooled!)
In many cases, the scammers will imply or threaten that unless the individual acts immediately, there will be negative repercussions, such as the shutdown of an account, legal charges, or other financial penalties, thereby playing on your sympathy response.
While many think these scams are easy to spot, the reality is that anyone can fall victim to them, unless they’ve undergone regular training on how to spot the techniques that attackers use. Below are five examples of Spear Phishing to be aware of.
Example 1. Fake websites
A cyber-criminal will design a carefully-worded phishing email which includes a link to a spoofed version of a popular website. The website imitates the layout of the original site to trick the victim into entering their account credentials.
Example 2. CEO Fraud
An attacker will take control of an email address familiar to the employee, such as their company’s CEO, Human Resources Manager, or IT admin. The hacker will assume this individual’s identity and ask the user to complete an urgent action, such as transferring funds, updating their personal information, or installing a new app.
Example 3. Malware
In these types of phishing attacks, an attacker will try to trick an employee into clicking on a malicious email attachment. Usually, this type of attack is carried out with a fake invoice or delivery notification.
If you think that the email may be legit, go to a link that you know is safe (one that you have save for the company) and log in from there. Or, you can always call the company and confirm or deny the validity of the email you received.
REMEMBER
If you don't recognize the sender, NEVER click on the attachments or links!
Example 4. Smishing
An SMS-based phishing attack in which a hacker will send an SMS or voice message asking the recipient to click on a link to accept a gift, change your password or call a number. The link will take them to a phishing website that they will use to try and gather more information from you.
Also, the link you click on could have malware in it. What does that mean? It could install a program on your phone that will allow the hacker to gain access to all your personal information, e.g. contacts, passwords, email, photos.

Example 5. Vishing
An unknown caller will call the victim and or leave a voicemail urging them to phone them back and hand over personal information, usually by impersonating someone from a trusted company.
The most common type of this is a Tech Support Call.
This attack is widespread in large companies where employees might not know or have met members of the tech support department. Scammers will pretend they need to do a computer update or repair and ask for the victim’s password to do it.
Education is key to beating these attacks. Frequently remind users that you will never ask them to divulge their password over the phone and that they shouldn’t do so under any circumstance.
Security Awareness Week 4: Passphrases and Canary Files
Zero Trust System
CIS is striving to get as close as possible to Zero Trust security system to secure infrastructure and data across SPU's network. A Zero Trust System requires all users to be authenticated and continuously validated for security configuration before being granted access into SPU's system.
A Zero Trust system is a framework that aims to prevent data breaches from both inside and outside the network. Since only individuals who have been authenticated and authorized for SPU's network can access entry points, adhering to this system provides an added layer of protection for all sensitive data that SPU stewards and prevents unauthorized access to easily accessible entry points.
This framework does not imply that SPU and/or CIS do not trust their students and employees, but rather acknowledges that breaches can occur from anywhere. This system is designed to prevent such incidents.
Multi-Factor Authentication (or MFA)
MFA is one facet of this system to help protect the SPU network and its users. All SPU users must link their SPU accounts with the Microsoft Authorization app on their phones. When students and employees sign into their accounts, SPU will automatically work to verify that the individual logging into the account has been authorized before granting access.
To make logging in easier and more efficient, keep your phone on hand so that you will be able to immediately verify your identity.

Creating a Strong Passphrase
It is also important for users to use a strong Passphrase or password for securing your account. A strong password will protect your account while also not containing any personally identifiable words; like your mother's maiden name or your childhood pet. It is also important to use a strong or complex password, as a more simple passphrase can be easily guessed.
Here are some key things to follow when creating a password:
Use a combination of numbers, capitalization and special characters.
Use a longer passphrase that you can easily remember.
Don't use a password you have used before, or a slight variation of a pre-existing password.


Do NOT write down OR your share your SPU password with anyone.
Password Managing
If you are worried about keeping track of your passwords, use a password manager that will keep track and record all of your passwords and where they are used. It is also likely that your phone or Google account will have password tracking enabled.
For more information on SPU's Password Policies, please select here.
Canary Files
Canary files are false or fake files with anti-malware software embedded within them that notifies the user when there has been a breach in your device's security. The files are similar to normal files that would typically be stored on a device by a user.
The normal user will not normally access these files and instead they are acting as a form of bait for files that may be seen as valuable to cyber-criminals. Just like the practice of using canaries in coal mines to signal when it was safe for miners to work, Canary files exist as a prevention method against malware (including ransomware).
There have been rare cases of SPU employees discovering canary files on their device. If you come across canary files on your device, please contact the HelpDesk at (206) 281-2982 or at help@spu.edu for further assistance

Cybersecurity Awareness Month Quizzes
Thank you for joining us for this year's Cybersecurity Awareness month as we covered Phishing, Ransomware, Social Engineering (Spear Phishing), Passphrases, and Canary Files.
If you have questions or concerns about the topics covered, or would like to learn more, a student technician with the HelpDesk would be more than happy to assist! You can contact the HelpDesk by phone at 206.281.2982 or by email at help@spu.edu.
As a reminder, we are offering one quiz for Faculty and Staff and one quiz for Students to test their knowledge on the topics we covered this month. The quiz will remain open until November 15th, 2023.
A Few Rules to Follow:
One quiz attempt per individual.
A student may not take the employee quiz and employees may not take the student quiz.
Only scores of 100% will be automatically entered into the raffle.
Prizes will only be given out to the winning individual(s) after they have made their *selection.
One prize per winner.
*Raffle winners will be contacted by CIS and choose their prize from the available options. Options include bluetooth speakers and/or gift cards.